Best Way to Disinfect Razor to Use Again
Over the concluding few months, I've seen a countersign strength meter on nearly every signup form I've encountered. Password forcefulness meters are on fire.
Here'south a question: does a meter actually aid people secure their accounts? It's less of import than other areas of spider web security, a short sample of which include:
- Preventing online slap-up with throttling or CAPTCHAs.
- Preventing offline cracking past selecting a suitably slow hash function with user-unique salts.
- Securing said countersign hashes.
With that disclaimer — yes. I'k convinced these metershave the potential to help. Co-ordinate to Mark Burnett'south 2006 volume,Perfect Passwords: Selection, Protection, Hallmark, which counted frequencies from a few meg passwords over a variety of leaks, ane in 9 people had a password in this peak 500 list. These passwords include some real stumpers: password1, compaq, 7777777, merlin, rosebud. Burnett ran a more recent study last year, looking at half-dozen one thousand thousand passwords, and institute an insane 99.8% occur in the tiptop 10,000 list, with 91% in the peak 1,000. The methodology and bias is an important qualifier — for instance, since these passwords mostly come from croaky hashes, the listing is biased towards crackable passwords to begin with.
These are only the really like shooting fish in a barrel-to-gauge passwords. For the residual, I'd wager a large percent are nonetheless predictable plenty to be susceptible to a minor online attack. And then I do think these meters could help, by encouraging stronger countersign decisions through direct feedback. But correct now, with a few closed-source exceptions, I believe they more often than not hurt. Here'south why.
Strength is all-time measured as entropy, in bits: it's the number of times a space of possible passwords tin can be cut in half. A naive strength interpretation goes like this:
# due north: password length # c: password cardinality: the size of the symbol space # (26 for lowercase letters only, 62 for a mix of lower+upper+numbers) entropy = northward * lg(c) # base ii log This brute-strength analysis is accurate for people who choose random sequences of letters, numbers and symbols. But with few exceptions (shoutout to 1Password / KeePass), people of grade choose patterns — dictionary words, spatial patterns similar qwerty , asdf or zxcvbn , repeats like aaaaaaa , sequences similar abcdef or 654321 , or some combination of the above. For passwords with capital letters, odds are information technology's the first letter of the alphabet that's uppercase. Numbers and symbols are often predictable too: l33t speak (3 for e, 0 for o, @ or 4 for a), years, dates, aught codes, and so on.
As a outcome, simplistic strength estimation gives bad advice. Without checking for common patterns, the practise of encouraging numbers and symbols means encouraging passwords that might only be slightly harder for a computer to crack, and yet frustratingly harder for a man to remember. xkcd nailed information technology:
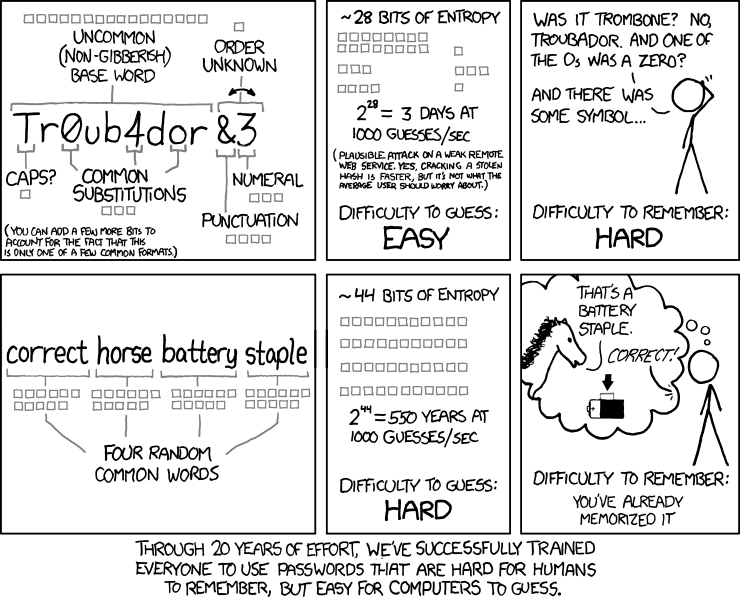
As an independent Dropbox hackweek project, I thought it'd be fun to build an open up source estimator that catches common patterns, and as a corollary, doesn't penalize sufficiently complex passphrases similar correcthorsebatterystaple. It's now live on dropbox.com/annals and bachelor for use on github. Endeavor the demo to experiment and see several instance estimations.
The table below compares zxcvbn to other meters. The indicate isn't to dismiss the others — countersign policy is highly subjective — rather, it's to give a better movie of how zxcvbn is different.
A few notes:
- I took these screenshots on Apr third, 2012. I needed to crop the bar from the gmail signup form to make it fit in the table, making the departure in relative width more pronounced than on the form itself.
- zxcvbn considers
correcthorsebatterystaplethe strongest countersign of the 3. The rest either consider it the weakest or disallow it. (Twitter gives about the same score for each, but if you squint, the scores are slightly different.) - zxcvbn considers
qwER43@!weak considering it's a brusk QWERTY design. It adds extra entropy for each turn and shifted graphic symbol. - The PayPal meter considers
qwER43@!weak butaaAA11!!strong. Speculation, but that might exist considering it detects spatial patterns likewise. - Bank of America doesn't allow passwords over xx characters, disallowing
correcthorsebatterystaple. Passwords tin contain some symbols, but not&or!, disallowing the other ii passwords. eBay doesn't allow passwords over 20 characters either. - Few of these meters appear to employ the naive estimation I opened with; otherwise
correcthorsebatterystaplewould have a high rating from its long length. Dropbox used to add points for each unique lowercase letter, upper-case letter alphabetic character, number, and symbol, up to a certain cap for each group. This mostly has the same only-works-for-brute-strength problem, although information technology as well checked against a common passwords lexicon. I don't know the details backside the other meters, but a scoring checklist is another common approach (which also doesn't check for many patterns). - I picked Troubadour to be the base discussion of the 2nd column, not Troubador as occurs in xkcd, which is an uncommon spelling.
Installation
zxcvbn has no dependencies and works on ie7+/opera/ff/safari/chrome. The best mode to add it to your registration page is:
<script type="text/javascript" src="zxcvbn-async.js"> </script> zxcvbn-async.js is a beggarly 350 bytes. On window.load, subsequently your folio loads and renders, it'll load zxcvbn.js, a fatty 680k (320k gzipped), most of which is a dictionary. I haven't found the script size to be an issue; since a password is ordinarily non the get-go thing a user enters on a signup grade, at that place'south plenty of fourth dimension to load.
zxcvbn adds a single role to the global namespace:
zxcvbn(countersign, user_inputs) It takes ane required argument, a password, and returns a result object. The outcome includes a few properties:
issue.entropy # bits result.crack_time # interpretation of actual crack time, in seconds. result.crack_time_display # same cleft time, every bit a friendlier string: # "instant", "6 minutes", "centuries", etc. result.score # 0, one, 2, 3 or four if scissure time is less than # 10**two, 10**4, 10**6, 10**eight, Infinity. # (helpful for implementing a strength bar.) result.match_sequence # the detected patterns used to summate entropy. outcome.calculation_time # how long it took to calculate an answer, # in milliseconds. normally only a few ms. The optional user_inputs argument is an array of strings that zxcvbn will add to its internal dictionary. This tin can exist whatever listing of strings you like, simply it's meant for user inputs from other fields of the form, like name and email. That way a password that includes the user'due south personal info can be heavily penalized. This list is also good for site-specific vocabulary. For case, ours includes dropbox .
zxcvbn is written in CoffeeScript. zxcvbn.js and zxcvbn-async.js are unreadably closure-compiled, but if you'd like to extend zxcvbn and send me a pull request, the README has development setup info.
The residue of this post details zxcvbn'due south design.
The model
zxcvbn consists of three stages: match, score, then search.
- match enumerates all the (possibly overlapping) patterns it can detect. Currently zxcvbn matches against several dictionaries (English language words, names and surnames, Burnett's 10,000 mutual passwords), spatial keyboard patterns (QWERTY, Dvorak, and keypad patterns), repeats (aaa), sequences (123, gfedcba), years from 1900 to 2019, and dates (3-thirteen-1997, 13.3.1997, 1331997). For all dictionaries, match recognizes uppercasing and common l33t substitutions.
- score calculates an entropy for each matched design, contained of the remainder of the password, bold the attacker knows the blueprint. A simple example: rrrrr. In this example, the attacker needs to iterate over all repeats from length 1 to five that start with a lowercase letter of the alphabet:
entropy = lg(26*5) # most vii $.25 - search is where Occam's razor comes in. Given the full prepare of possibly overlapping matches, search finds the simplest (lowest entropy) non-overlapping sequence. For example, if the password is
damnation, that could be analyzed as 2 words,damandnation, or as one. It's important that information technology be analyzed as one, because an attacker trying lexicon words will fissure it as one discussion long before ii. (As an aside, overlapping patterns are also the primary agent backside accidentally tragic domain name registrations, likechildrens-laughter.comonly without the hyphen.)
Search is the crux of the model. I'll start there and work backwards.
Minimum entropy search
zxcvbn calculates a password'south entropy to be the sum of its constituent patterns. Any gaps betwixt matched patterns are treated every bit brute-force "patterns" that also contribute to the full entropy. For example:
entropy("stockwell4$eR123698745") == surname_entropy("stockwell") + bruteforce_entropy("iv$eR") + keypad_entropy("123698745") That a password's entropy is the sum of its parts is a big assumption. However, it's a conservative assumption. Past disregarding the "configuration entropy" — the entropy from the number and arrangement of the pieces — zxcvbn is purposely underestimating, past giving a password's structure away for free: It assumes attackers already know the construction (for example,surname-bruteforce-keypad), and from there, information technology calculates how many guesses they'd need to iterate through. This is a meaning underestimation for complex structures. Considering correcthorsebatterystaple,word-discussion-word-word, an assaulter running a program like L0phtCrack or John the Ripper would typically endeavor many simpler structures first, such asword,discussion-number, orgive-and-take-word, before reachingword-word-word-give-and-take. I'thou OK with this for iii reasons:
- It's difficult to formulate a audio model for structural entropy; statistically, I don't happen to know what structures people cull most, and then I'd rather do the prophylactic matter and underestimate.
- For a complex structure, the sum of the pieces alone is often sufficient to give an "splendid" rating. For example, fifty-fifty knowing theword-give-and-take-word-word construction of correcthorsebatterystaple, an assaulter would need to spend centuries cracking it.
- Nearly peopledon't take circuitous password structures. Disregarding structure only underestimates past a few bits in the common case.
With this assumption out of the way, hither's an efficient dynamic programming algorithm in CoffeeScript for finding the minimum not-overlapping match sequence. It runs inO(north·1000) fourth dimension for a length-due north countersign withm (maybe overlapping) candidate matches.
# matches: the password's full array of candidate matches. # each lucifer has a starting time alphabetize (friction match.i) and an end index (match.j) into # the password, inclusive. minimum_entropy_match_sequence = (countersign, matches) -> # e.chiliad. 26 for lowercase-but bruteforce_cardinality = calc_bruteforce_cardinality countersign up_to_k = [] # minimum entropy up to 1000. backpointers = [] # for the optimal sequence of matches up to k, # holds the final match (match.j == k). # zip means the sequence ends w/ a animate being-strength char for k in [0...password.length] # starting scenario to try to trounce: # calculation a beast-force character to the minimum entropy sequence at k-one. up_to_k[yard] = (up_to_k[k-i] or 0) + lg bruteforce_cardinality backpointers[chiliad] = nix for friction match in matches when match.j == g [i, j] = [match.i, match.j] # see if minimum entropy up to i-ane + entropy of this match is less # than the electric current minimum at j. candidate_entropy = (up_to_k[i-1] or 0) + calc_entropy(match) if candidate_entropy < up_to_k[j] up_to_k[j] = candidate_entropy backpointers[j] = match # walk backwards and decode the all-time sequence match_sequence = [] g = password.length - 1 while k >= 0 match = backpointers[k] if friction match match_sequence.push match k = friction match.i - 1 else chiliad -= 1 match_sequence.reverse() # fill in the blanks between pattern matches with bruteforce "matches" # that way the lucifer sequence fully covers the password: # match1.j == match2.i - 1 for every next match1, match2. make_bruteforce_match = (i, j) -> pattern: 'bruteforce' i: i j: j token: password[i..j] entropy: lg Math.pow(bruteforce_cardinality, j - i + 1) cardinality: bruteforce_cardinality k = 0 match_sequence_copy = [] for match in match_sequence # fill up gaps in the heart [i, j] = [match.i, lucifer.j] if i - k > 0 match_sequence_copy.push button make_bruteforce_match(k, i - 1) one thousand = j + 1 match_sequence_copy.push match if k < password.length # make full gap at the end match_sequence_copy.push make_bruteforce_match(k, password.length - 1) match_sequence = match_sequence_copy # or 0 corner case is for an empty password '' min_entropy = up_to_k[password.length - one] or 0 crack_time = entropy_to_crack_time min_entropy # terminal result object password: countersign entropy: round_to_x_digits min_entropy, 3 match_sequence: match_sequence crack_time: round_to_x_digits crack_time, 3 crack_time_display: display_time crack_time score: crack_time_to_score crack_time backpointers[j] holds the match in this sequence that ends at password position j, or null if the sequence doesn't include such a lucifer. Typical of dynamic programming, constructing the optimal sequence requires starting at the finish and working backwards.
Especially considering this is running browser-side as the user types, efficiency does thing. To get something up and running I started with the simpler O(2m) approach of calculating the sum for every possible not-overlapping subset, and it slowed downwards rapidly. Currently all together, zxcvbn takes no more than a few milliseconds for nigh passwords. To requite a rough ballpark: running Chrome on a two.four GHz Intel Xeon, correcthorsebatterystaple took about 3ms on boilerplate.coRrecth0rseba++ery9/23/2007staple$ took well-nigh 12ms on average.
Threat model: entropy to crack time
Entropy isn't intuitive: How exercise I know if 28 $.25 is strong or weak? In other words, how should I go from entropy to actual estimated crack time? This requires more assumptions in the class of a threat model. Allow's presume:
- Passwords are stored as salted hashes, with a different random table salt per user, making rainbow attacks infeasible.
- An assailant manages to steal every hash and salt. The assailant is at present guessing passwords offline at max rate.
- The assailant has several CPUs at their disposal.
Hither'due south some back-of-the-envelope numbers:
# for a hash function like bcrypt/scrypt/PBKDF2, 10ms is a prophylactic lower bound # for one guess. commonly a gauge would take longer -- this assumes fast # hardware and a small work factor. conform for your site accordingly if yous # use some other hash function, peradventure past several orders of magnitude! SINGLE_GUESS = .010 # seconds NUM_ATTACKERS = 100 # number of cores guessing in parallel. SECONDS_PER_GUESS = SINGLE_GUESS / NUM_ATTACKERS entropy_to_crack_time = (entropy) -> .5 * Math.pow(2, entropy) * SECONDS_PER_GUESS I added a .5 term because we're measuring the average cleft time, non the time to try the full space.
This math is perhaps overly safety. Big-calibration hash theft is a rare ending, and unless you're being specifically targeted, it's unlikely an assaulter would dedicate 100 cores to your single password. Normally an attacker has to guess online and bargain with network latency, throttling, and CAPTCHAs.
Entropy adding
Upward next is how zxcvbn calculates the entropy of each constituent pattern. calc_entropy() is the entry signal. It's a simple dispatch:
calc_entropy = (match) -> return match.entropy if match.entropy? entropy_func = switch match.design when 'echo' so repeat_entropy when 'sequence' then sequence_entropy when 'digits' and so digits_entropy when 'twelvemonth' then year_entropy when 'engagement' then date_entropy when 'spatial' then spatial_entropy when 'dictionary' then dictionary_entropy match.entropy = entropy_func match I gave an outline before for how repeat_entropy works. You can see the full scoring code on github, only I'll describe two other scoring functions here to give a taste: spatial_entropy and dictionary_entropy.
Consider the spatial design qwertyhnm. It starts at q, its length is nine, and it has 3 turns: the initial turn moving right, then down-correct, and then correct. To parameterize:
south # number of possible starting characters. # 47 for QWERTY/Dvorak, 15 for pc keypad, 16 for mac keypad. L # password length. Fifty >= 2 t # number of turns. t <= 50 - 1 # for instance, a length-3 countersign tin can have at almost 2 turns, like "qaw". d # average "degree" of each central -- the number of adjacent keys. # about 4.6 for QWERTY/Dvorak. (1000 has half dozen neighbors, tilda only has 1.) The space of total possibilities is so all possible spatial patterns of length L or less with t turns or less:
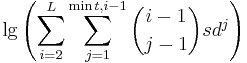
(i – one) cull (j – ane) counts the possible configurations of turn points for a length-i spatial design withj turns. The -one is added to both terms because the first turn always occurs on the first letter of the alphabet. At each ofj turns, in that location'sd possible directions to go, for a total ofdj possibilities per configuration. An assailant would demand to try each starting graphic symbol too, hence thes. This math is only a crude approximation. For example, many of the alternatives counted in the equation aren't really possible on a keyboard: for a length-5 pattern with 1 plow, "start at q moving left" gets counted, but isn't really possible.
CoffeeScript allows natural expression of the higher up:
lg = (north) -> Math.log(n) / Math.log(ii) nPk = (n, k) -> render 0 if k > due north outcome = ane result *= k for 1000 in [north-grand+one..northward] result nCk = (northward, k) -> return ane if m == 0 k_fact = 1 k_fact *= m for g in [i..k] nPk(n, k) / k_fact spatial_entropy = (match) -> if match.graph in ['qwerty', 'dvorak'] s = KEYBOARD_STARTING_POSITIONS d = KEYBOARD_AVERAGE_DEGREE else s = KEYPAD_STARTING_POSITIONS d = KEYPAD_AVERAGE_DEGREE possibilities = 0 50 = match.token.length t = match.turns # estimate num patterns w/ length L or less and t turns or less. for i in [two..L] possible_turns = Math.min(t, i - 1) for j in [i..possible_turns] possibilities += nCk(i - one, j - 1) * s * Math.prisoner of war(d, j) entropy = lg possibilities # add extra entropy for shifted keys. (% instead of 5, A instead of a.) # math is like to extra entropy from uppercase letters in dictionary # matches, run into the next snippet below. if friction match.shifted_count Southward = lucifer.shifted_count U = match.token.length - match.shifted_count # unshifted count possibilities = 0 possibilities += nCk(S + U, i) for i in [0..Math.min(S, U)] entropy += lg possibilities entropy On to lexicon entropy:
dictionary_entropy = (lucifer) -> entropy = lg lucifer.rank entropy += extra_uppercasing_entropy lucifer entropy += extra_l33t_entropy friction match entropy The starting time line is the well-nigh of import: The match has an associated frequency rank, where words likethe andgood have low rank, and words likephotojournalist andmaelstrom have high rank. This lets zxcvbn scale the calculation to an appropriate lexicon size on the fly, because if a countersign contains but common words, a cracker can succeed with a smaller dictionary. This is one reason why xkcd and zxcvbn slightly disagree on entropy for correcthorsebatterystaple (45.two bits vs 44). The xkcd instance used a fixed dictionary size of two 11 (about 2k words), whereas zxcvbn is adaptive. Adaptive sizing is also the reason zxcvbn.js includes entire dictionaries instead of a space-efficient Bloom filter — rank is needed in improver to a membership test.
I'll explain how frequency ranks are derived in the information section at the stop. Uppercasing entropy looks like this:
extra_uppercase_entropy = (match) -> word = lucifer.token return 0 if word.friction match ALL_LOWER # a capitalized word is the most common capitalization scheme, # so information technology only doubles the search space (uncapitalized + capitalized): # 1 extra bit of entropy. # allcaps and stop-capitalized are common enough too, # underestimate every bit i extra bit to be rubber. for regex in [START_UPPER, END_UPPER, ALL_UPPER] return ane if word.friction match regex # otherwise calculate the number of ways to capitalize # U+L uppercase+lowercase letters with U uppercase messages or less. # or, if in that location's more than uppercase than lower (for e.thou. PASSwORD), the number # of means to lowercase U+L messages with L lowercase letters or less. U = (chr for chr in discussion.divide('') when chr.lucifer /[A-Z]/).length L = (chr for chr in word.split('') when chr.match /[a-z]/).length possibilities = 0 possibilities += nCk(U + L, i) for i in [0..Math.min(U, Fifty)] lg possibilities And so, 1 extra flake for kickoff-letter-capital letter and other common capitalizations. If the uppercasing doesn't fit these mutual molds, it adds:
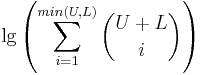
The math for l33t substitution is similar, but with variables that count substituted and unsubstituted characters instead of uppers and lowers.
Blueprint matching
So far I covered pattern entropy, just not how zxcvbn finds patterns in the first place. Dictionary friction match is straightforward: check every substring of the password to run into if it's in the dictionary:
dictionary_match = (password, ranked_dict) -> consequence = [] len = countersign.length password_lower = password.toLowerCase() for i in [0...len] for j in [i...len] if password_lower[i..j] of ranked_dict word = password_lower[i..j] rank = ranked_dict[discussion] result.push( blueprint: 'dictionary' i: i j: j token: password[i..j] matched_word: word rank: rank ) event ranked_dict maps from a word to its frequency rank. It'due south similar an array of words, ordered by high-frequency-kickoff, but with index and value flipped. l33t substitutions are detected in a separate matcher that uses dictionary_match as a archaic. Spatial patterns similar bvcxz are matched with an adjacency graph approach that counts turns and shifts forth the style. Dates and years are matched with regexes. Hit matching.coffee on github to read more.
Data
As mentioned earlier, the 10k password list is from Burnett, released in 2011.
Frequency-ranked names and surnames come up from the freely available 2000 US Census. To assistance zxcvbn not crash ie7, I cut off the surname dictionary, which has a long tail, at the 80th percentile (meaning 80% of Americans have one of the surnames in the list). Mutual first names include the 90th percentile.
The 40k frequency listing of English words comes from a project on Wiktionary, which counted about 29M words across US television set and movies. My hunch is that of all the lists I could find online, tv set and pic scripts will capture popular usage (and hence likely words used in passwords) better than other sources of English, but this is an untested hypothesis. The list is a flake dated; for example, Frasier is the 824 thursday most common discussion.
Decision
At first glance, building a good figurer looks about as hard as edifice a good cracker. This is true in a tautological sort of mode if the goal is accuracy, because "platonic entropy" — entropy co-ordinate to a perfect model — would measure exactly how many guesses a given cracker (with a smart operator backside it) would demand to take. The goal isn't accuracy, though. The goal is to give audio password advice. And this actually makes the job a bit easier: I can have the liberty of underestimating entropy, for case, with the simply downside of encouraging passwords that are stronger than they need to be, which is frustrating but non dangerous.
Good estimation is still difficult, and the main reason is in that location's and then many different patterns a person might use. zxcvbn doesn't take hold of words without their first letter, words without vowels, misspelled words, n-grams, zipcodes from populous areas, disconnected spatial patterns like qzwxec, and many more. Obscure patterns (like Catalan numbers) aren't important to grab, only for each common design that zxcvbn misses and a cracker might know almost, zxcvbn overestimates entropy, and that's the worst kind of bug. Possible improvements:
- zxcvbn currently only supports English words, with a frequency list skewed toward American usage and spelling. Names and surnames, coming from the US census, are also skewed. Of the many keyboard layouts in the world, zxcvbn recognizes but a few. Improve country-specific datasets, with an option to choose which to download, would be a large improvement.
- As this written report past Joseph Bonneau attests, people often choose common phrases in addition to common words. zxcvbn would be better if it recognized "Harry Potter" as a mutual phrase, rather than a semi-common name and surname. Google's n-gram corpus fits in a terabyte, and even a good bigram list is impractical to download browser-side, so this functionality would require server-side evaluation and infrastructure toll. Server-side evaluation would also let a much larger single-discussion dictionary, such as Google'due south unigram set.
- Information technology'd be better if zxcvbn tolerated misspellings of a give-and-take up to a certain edit distance. That would bring in many discussion-based patterns, like skip-the-showtime-letter. It'south hard because word segmentation gets catchy, especially with the added complexity of recognizing l33t substitutions.
Fifty-fifty with these shortcomings, I believe zxcvbn succeeds in giving better password advice in a world where bad password decisions are widespread. I promise you lot find it useful. Please fork on github and have fun!
Big thanks to Chris Varenhorst, Gautam Jayaraman, Ben Darnell, Alicia Chen, Todd Eisenberger, Kannan Goundan, Chris Beckmann, Rian Hunter, Brian Smith, Martin Baker, Ivan Kirigin, Julie Tung, Tido the Great, Ramsey Homsany, Bart Volkmer and Sarah Niyogi for helping review this postal service.
Source: https://dropbox.tech/security/zxcvbn-realistic-password-strength-estimation
0 Response to "Best Way to Disinfect Razor to Use Again"
Post a Comment